Managed IT support services play a critical role in helping law and accounting firms maintain efficiency in their daily operations. These industries…
ISC provides managed IT services designed to prevent problems before they disrupt your operations. Our team monitors your systems continuously, maintains infrastructure, and ensures your technology environment remains stable and secure. Instead of reacting to IT problems after they occur, we focus on preventing them entirely.
ISC delivers proactive IT support, cybersecurity protection, and compliance expertise for law firms, accounting firms, government contractors, and growing businesses across Northern Virginia.














Policies, Procedures, SSPs & Catalogues Developed by ISC Experts
Audit Supported across ISO, CMMC, NIST, GovRAMP and FedRAMP
Domain-Based Training across AI, HIPAA, Phishing & Security Policies
Security Standards & Frameworks including ISO, NIST, CMMC, FedRAMP, GovRAMP & HIPAA
Policies, Procedures, SSPs & Catalogues Developed by ISC Experts
Client Engagement Across Multi Security Frameworks and Standards
Gap Assessments Completed across Diverse Environments to Strengthen Compliance
Compliance Success Rate through Effective Management & 27/7 Oversight
Policies, Procedure, SSPs & Catalogues Developed by ISC experts
Audits Supported across ISO, CMMC, NIST, GovRAMP and FedRAMP
Domain-based trainings developed across AI, HIPAA, Phishing and Security Policies
Security Standards and Frameworks Expertise including ISO, NIST, CMMC, FedRAMP, GovRAMP and HIPAA
Audit Readiness through Continuous Monitoring and Effective Program Management
Client Engagements Across Multi Security Frameworks and Standards
Gap assessments completed across diverse environments to strengthen compliance
Compliance Success Rate through Effective Compliance Management and 24/7 Oversight
Policies, Procedure, SSPs & Catalogues Developed by ISC experts
Audits Supported across ISO, CMMC, NIST, GovRAMP and FedRAMP
Domain-based trainings developed across AI, HIPAA, Phishing and Security Policies
Security Standards and Frameworks Expertise including ISO, NIST, CMMC, FedRAMP, GovRAMP and HIPAA
Audit Readiness through Continuous Monitoring and Effective Program Management
Client Engagements Across Multi Security Frameworks and Standards
Gap assessments completed across diverse environments to strengthen compliance
Compliance Success Rate through Effective Compliance Management and 24/7 Oversight
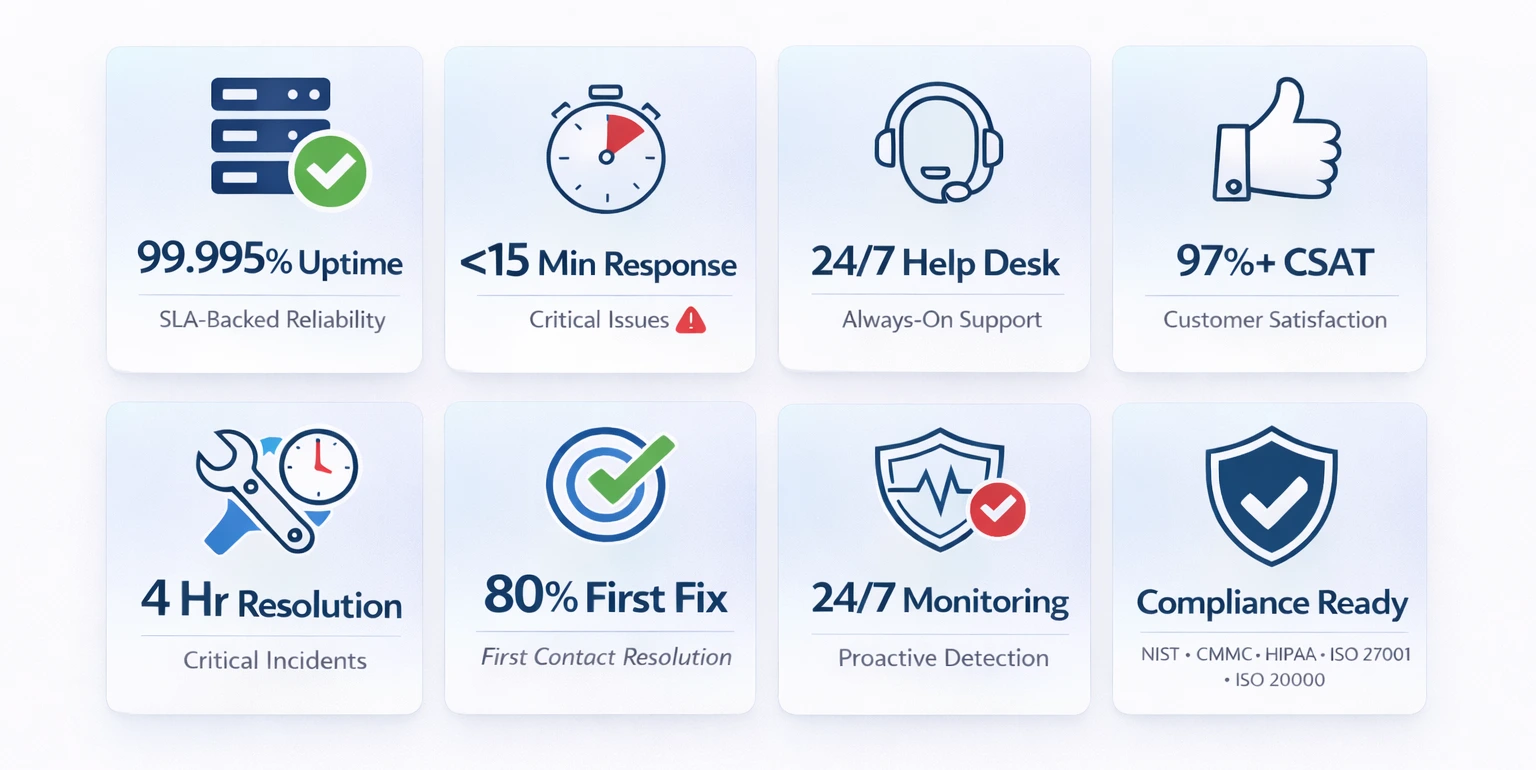
SLA-Backed Reliability
Critical Issues
Always-On Support
Customer Satisfaction
Critical Incidents
First Contact Resolution
Proactive Detection
NIST • CMMC • HIPAA • ISO 27001 • ISO 20000
Organizations across Northern Virginia trust ISC to secure and manage their technology environments. We support law firms, accounting firms, government contractors, healthcare providers, and growing small businesses with reliable IT infrastructure, strong cybersecurity, and responsive support.
By partnering with ISC, businesses gain experienced technology professionals who build secure, stable, and scalable environments
Organizations across Northern Virginia trust ISC to manage and secure their technology environments. Our engineers work with professional organizations that require dependable IT infrastructure, strong cybersecurity protections, and responsive support.
Industries commonly supported include law firms, accounting firms, government contractors, healthcare providers, and growing small businesses. Each of these industries depends heavily on secure technology systems and reliable IT operations.
When businesses partner with ISC, they gain access to experienced technology professionals who understand how to design secure, stable, and scalable infrastructure environments.
ISC provides comprehensive managed IT services designed to keep your systems operating efficiently. Our proactive monitoring systems continuously observe your network, servers, and endpoints to identify potential problems before they cause disruptions. Routine maintenance, software updates, and infrastructure optimization ensure your technology environment remains stable and reliable.
Employees rely on technology to complete their work every day. When issues arise, productivity slows and frustration increases. ISC provides responsive help desk support that resolves problems quickly. Our engineers assist users with software issues, device troubleshooting, connectivity problems, and system access concerns.
Cyber threats continue to grow across every industry. Businesses of all sizes are potential targets for ransomware, phishing attacks, and data breaches. ISC implements layered cybersecurity protections including endpoint security, network monitoring, vulnerability management, and security best practices designed to protect sensitive data.
Organizations that handle sensitive data often face regulatory or cybersecurity framework requirements. ISC helps organizations strengthen their security posture while managing technology risk responsibly.
Law firms depend on secure technology systems to manage confidential client information, case files, and communications. ISC helps legal organizations maintain secure document systems, reliable networks, and strong cybersecurity protections designed specifically for legal environments.
Accounting firms process highly sensitive financial information and require dependable systems, especially during busy tax seasons. ISC supports accounting professionals with reliable infrastructure, secure data storage, and proactive monitoring that keeps systems running smoothly.
Government contractors frequently work with regulated data and must follow strict cybersecurity expectations. ISC helps these organizations maintain secure environments and implement security best practices that align with industry requirements.
Small businesses often lack dedicated internal IT teams but still depend on reliable technology environments. ISC delivers enterprise‑level IT support designed for growing organizations.
Proactive Monitoring
Our monitoring systems detect potential problems early so they can be resolved before they cause downtime.
Rapid Support Response
When technology issues occur, our engineers respond quickly to restore productivity.
Cybersecurity Expertise
Layered security protections help protect business data and reduce cyber risk.
Industry Experience
Our team understands the technology challenges faced by professional organizations.
Scalable Solutions
Our services adapt as your organization grows and technology needs evolve.

Hear from organisations that trust ISC to deliver reliable IT, cybersecurity, and compliance solutions that protect their business and support long-term success.
The team provided a customized solution tailored to ourspecific needs, ensuring our network remaine secure and our data protected. Their proactive approach and continuous support have given us the confidence to focus on growing our business without worrying about cyber threats.
The personalized IT solutions from ISC have improved our operational efficiency and data security, giving us peace of
mind. Highly recommend ISC for any organization seeking top-notch security solutions!
1SC’s cloud management services have transformed the way we handle data, providing secure and seamless integration across our platforms.
ISC helped us achieve full compliance with industry standards, significantly improving our security posture. Their cybersecurity expertise was instrumental in identifying vulnerabilities and implementing robust defense measures. The team provided a customized solutions.
SC helped us achieve full compliance with industry standards. Their cybersecurity expertise was instrumental in securing our network, Highly recommend ISC for any organization.

ISC reviews your existing technology environment and identifies key challenges affecting reliability or security.

Our engineers analyze your network, devices, systems, and cybersecurity protections.

ISC deploys monitoring systems, cybersecurity protections, and ongoing IT support to maintain stable operations.
If your organization is experiencing IT challenges, cybersecurity concerns, or infrastructure limitations, ISC can help. Our experts will review your environment and recommend improvements designed to strengthen reliability and security.
Fill out the form below, and we will contact you as soon as possible
A managed IT provider monitors and maintains business technology systems including servers, networks, cybersecurity protections, and user support.
ISC works with a wide range of organizations, including small businesses, law firms, healthcare providers, financial institutions, e-commerce companies, and government contractors. As a small business itself, ISC understands the unique resource constraints and risk profiles of growing organizations and tailors its solutions accordingly — whether you need full managed IT support, cybersecurity assessments, or regulatory compliance consulting.
ISC, short for Infosec Compliance, is a managed IT and cybersecurity firm based in Northern Virginia. ISC serves as a strategic partner for businesses of all sizes, providing proactive IT management, robust cybersecurity protection, and compliance support across frameworks such as FISMA, HIPAA, ISO 27001, CMMC, FedRAMP, and NIST 800-53. Rather than simply being a vendor, ISC works alongside your organization to reduce risk, improve operational resilience, and align technology with your growth goals.
Unlike large, impersonal IT firms, ISC offers direct access to its dedicated team of certified experts who take the time to understand your specific business environment. ISC takes a holistic approach that combines managed IT, network security, and compliance expertise in one place. This means you get consistent, personalized support — not a call center — and solutions that are designed around your operations, not a generic template.
Yes. ISC’s strength lies in its integrated approach. Many IT providers handle only infrastructure while compliance consultants work in isolation. ISC bridges both disciplines, offering certified engineers who can manage your IT environment while simultaneously guiding you through compliance requirements such as NIST 800-171, CMMC, ISO 27001, and HIPAA. This unified approach reduces duplicated effort, lowers cost, and ensures your technology controls align with your compliance obligations.
Law firms manage confidential client information that is highly valuable to cybercriminals.
Industries handling sensitive information such as legal, accounting, healthcare, and government contracting benefit greatly.
ISC has deep experience across healthcare, finance, legal, defense contracting, and e-commerce. The team is well-versed in sector-specific regulations — including HIPAA for healthcare, CMMC and NIST 800-171 for defense contractors, and PCI-DSS considerations for financial and e-commerce businesses. Each engagement is tailored to the client’s industry requirements and operational context.
ISC prioritizes long-term client partnerships over transactional engagements. Every client has direct access to the ISC team — not a rotating help desk — so the professionals supporting your business understand your environment intimately. ISC uses Service Level Agreements (SLAs) to ensure accountability and delivers proactive monitoring, regular reporting, and continuous improvement so your IT and security posture strengthens over time rather than stagnating.
Getting started is straightforward. Visit isccorp-us.com and use the contact form to schedule an initial consultation. ISC typically begins with an IT and/or cybersecurity assessment to understand your current environment, identify gaps, and develop a realistic roadmap. There is no obligation to commit before you understand exactly what support your organization needs and what it will cost.
Businesses across Northern Virginia rely on technology to operate efficiently and serve clients effectively. Managed IT services help organizations maintain reliable technology infrastructure while reducing operational risk.
ISC provides managed IT services that include proactive monitoring, infrastructure maintenance, cybersecurity protection, and technical support. Organizations such as law firms, accounting firms, and government contractors often require both reliable systems and strong cybersecurity protections.
By partnering with an experienced managed IT services provider, businesses gain access to engineers who monitor systems continuously and resolve problems quickly. This proactive approach helps prevent downtime and improves operational stability.
ISC provides managed IT services nationwide. However, for onsite presence, we serve the nation’s capital Washington, DC, and, Northern Virginia including:
Reliable technology infrastructure and strong cybersecurity are essential for modern organizations. ISC provides proactive managed IT services designed to keep your systems running efficiently while protecting sensitive business data.
Managed IT support services play a critical role in helping law and accounting firms maintain efficiency in their daily operations. These industries…
Introduction NIST 800-171 Compliance is essential for professional service firms that handle Controlled Unclassified Information (CUI). Ensuring compliance not
Introduction Law and accounting firms operate in highly regulated environments where data security, system uptime, and compliance are critical. Managed IT supp